Cybersecurity threats pose a grave challenge to the global economy, projected to inflict costs exceeding $10.5 trillion by 2023. This escalation underscores a rapidly evolving threat landscape, heightened by the sophisticated use of malware, ransomware, and phishing attacks leveraging artificial intelligence.
By 2024, proprietors will be required to steer through a growing range of cybersecurity issues, inclusive of internal threats and complex cyber assault strategies. Highlighting strong protective measures like multi-factor authentication, coding, and careful data distribution is pivotal in lessening threats and defending against identity fraud and deceptive electronic communications.
Decoding Cybersecurity Threats
The expansion of Internet of Things (IoT) technology considerably enlarges the potential for cyber attacks, anticipating a surge to around 30 billion devices by 2025. These devices, often lacking robust security measures, present numerous entry points for cybercriminals, making them prime targets for cyberattacks. To combat this, there is a growing emphasis on improving IoT security through enhanced protocols and rigorous testing.
Integration of AI in Cybersecurity
- Advanced Detection: AI and machine learning (ML) are increasingly integrated into cybersecurity solutions, providing the ability to swiftly analyze vast data sets, identify patterns, and detect anomalies that may indicate a security threat.
- Deepfake Detection: Investment in tools capable of identifying manipulated audio and video is crucial as the threat of realistic, AI-generated fake content grows.
Addressing State-Sponsored Cyberattacks
The rise in state-sponsored cyberattacks necessitates stronger international cooperation and cybersecurity defenses. These sophisticated attacks often target critical infrastructure and aim to steal sensitive data, making it imperative for nations and organizations to bolster their cybersecurity frameworks and share critical threat intelligence.
Emerging Cybersecurity Threats and Defensive Strategies
- AI-Powered Attacks: Cybercriminals are utilizing AI to enhance phishing campaigns and malware development, creating more sophisticated and hard-to-detect threats.
- Supply Chain Vulnerabilities: Attacks on supply chains remain a significant threat, with cybercriminals exploiting third-party vulnerabilities to infiltrate networks. Businesses must ensure rigorous security assessments and monitoring of all vendors.
- Legislative Actions: Fresh privacy regulations are coming into effect at the state level. For instance, the My Health My Data Act from Washington, as well as Oregon’s Consumer Privacy Act, are implementing more rigorous standards for data protection. These measures aim to reduce the likelihood of data breaches and strengthen the rights of consumers.
This evolving landscape underscores the necessity for businesses to adopt proactive cybersecurity measures, continuously update their security protocols, and remain vigilant against an ever-growing array of cyber threats.
Ransomware Attacks: Cybersecurity Threats
Ransomware continues to pose a significant threat to organizations globally, with attackers constantly refining their methods to bypass security measures. In 2024, businesses must be vigilant and proactive in implementing robust defenses against these evolving threats. Here are critical points to consider:
Key Trends and Tactics in Ransomware Attacks
- Sophistication and Success: Attacks are becoming more sophisticated, making it essential for organizations to enhance their backup and recovery strategies and educate employees on ransomware risks.
- Proactive Defense Measures: Regular data backups and network segmentation are crucial. These steps help minimize operational disruptions during an attack.
- Emerging Threats: Cybercriminals are increasingly using legitimate software and tools to execute attacks, highlighting the need for comprehensive security assessments of all network components.
Notable Ransomware Incidents and Responses
- VCURMS and STRRAT Malware Distribution: A phishing campaign recently spread these dangerous remote access trojans, signaling a shift in attack vectors.
- Significant Increase in Attacks: October 2023 saw a 66% spike in ransomware incidents compared to the previous year, emphasizing the growing threat.
- Global Impact: Ransomware is a worldwide issue, with attacks occurring across different continents, underscoring the need for global security strategies.
Evolution of Ransomware Tactics
- Triple Extortion: Attackers are not just encrypting data but also stealing it to leverage additional payment from victims.
- Use of AI and Deepfake: Advanced technologies are being employed to create more convincing phishing attacks, making it harder for users to identify threats.
- Shift Towards Encryption-Free Extortion: Increasing reliance on data theft before encryption indicates a strategic shift in ransomware attacks.
Understanding these dynamics is crucial for businesses to adapt their cybersecurity strategies effectively and mitigate the risks associated with ransomware.
Phishing Scams: Cybersecurity Threats
Phishing scams is Cybersecurity Threats continue to evolve, becoming increasingly sophisticated and personalized. Attackers now employ advanced tactics such as spear phishing, whaling, and the use of generative AI to craft convincing social engineering attacks. These methods are designed to bypass traditional security measures and exploit human vulnerabilities. Here are essential strategies and tips to mitigate these risks:
Key Prevention Strategies for Phishing Scams
- Educate and Train Employees: Continuous training on the latest phishing techniques and indicators is crucial. Employees should be taught to recognize suspicious emails, links, and requests.
- Implement Advanced Email Security Solutions: Utilizing AI-powered filters can help in detecting and blocking phishing attempts before they reach the user.
- Verify Contact Authenticity: Always confirm the legitimacy of the communication by directly contacting the supposed sender through official channels.
- Use Multi-Factor Authentication: MFA adds an extra layer of security, making it harder for attackers to gain unauthorized access even if they have the password.
- Regularly Update and Patch Systems: Keeping software and security systems updated closes vulnerabilities that could be exploited by attackers.
Advanced Phishing Techniques and Countermeasures
- AI and Generative AI in Phishing: Attackers use AI to improve the authenticity of phishing emails by enhancing grammar and spelling. Awareness and advanced spam filters trained to recognize these nuances are essential.
- Deepfake Technology: This AI-generated content is becoming a tool in phishing scams, used to create fake audio or video clips. Implementing technology to detect deepfakes is becoming increasingly important.
- Behavioral Analysis and Anomaly Detection: Employing systems that analyze user behavior and detect anomalies can help in identifying and responding to phishing attempts in real time.
Businesses must stay vigilant and proactive, updating their cybersecurity strategies to include these advanced defenses against the ever-evolving phishing threats.
Insider Cybersecurity Threats
Insider Cybersecurity threats represent a critical security issue, with 74% of organizations experiencing moderate to high impacts in 2023. The financial repercussions have surged by 44% over the past two years, showcasing nearly 1 billion records compromised by insiders. These threats stem from individuals within the organization—whether due to malicious intent or negligence—misusing their access to harm the organization.
Types and Examples of Insider Threats
- Direct Threats: Involves explicit inappropriate actions like unauthorized access or data theft.
- Indirect Threats: Includes subtle behavioral patterns that may signal potential risks, such as unusual access patterns or unexplained data transfers.
Common Insider Actions Leading to Threats
- Violations of safety protocols
- Unnecessary requests for elevated access
- Misuse of social media and external storage systems
- Retention of access post-termination
Profiles of Insider Threats
- Malicious Insiders: Former or current employees who intentionally breach security.
- Negligent Insiders: Employees whose careless actions compromise security.
- Third-Party Insiders: External actors who gain unauthorized access, often through means like VPNs.
Motivations Behind Insider Threats
Motivations range from financial gain and personal vendettas to espionage and mere ignorance. Understanding these can help tailor more effective prevention strategies.
Managing Insider Threats: Benefits and Challenges
- Benefits: Quick incident response, identification of high-risk profiles, effective organizational control.
- Challenges: Issues like delayed detection and maintaining privacy while monitoring activities.
Best Practices in Insider Cybersecurity Threat Management
- Conduct regular IT security training.
- Monitor user activities and behaviors.
- Implement risk reduction strategies through employee categorization.
- Increase transparency across all organizational levels.
The rise of BYOD cultures and third-party services has exacerbated insider threats, making robust monitoring and detection systems essential. The rising relevance of the Zero Trust cybersecurity structure, premised on a default position of no trust for any entity, is indicative of the landscape in 2024. This approach is being adopted by businesses seeking to efficiently mitigate both intentional and inadvertent internal threats.
Advancements in Cybersecurity Threats Tactics
Brute Force and Credential Attacks
- Increasing Use of Brute Force Tactics: Malicious actors are employing methods like credential stuffing and password spraying more frequently. These brute force attacks attempt to access secure systems by guessing passwords, often using stolen data lists.
- Mitigation Strategies: Implementing robust identity and access management solutions is critical. This includes enforcing strong password policies, multifactor authentication (MFA), and continuous monitoring of network activities.
IoT and Mobile Security Enhancements to tackle Cybersecurity Threats
- Device Security Measures: Prioritizing security for Internet of Things (IoT) devices is crucial due to their vulnerability and widespread use. Regular patching, network segmentation, and modern authentication methods must be adopted.
- Mobile Device Management (MDM): With the rise of Bring Your Own Device (BYOD) policies, robust MDM solutions are necessary to manage and secure employee mobile devices effectively.
Cloud and Third-Party Security Management to tackle Cybersecurity Threats
- Cloud Governance: Implementing a mature cloud governance model addresses numerous security challenges, including misconfigurations and compliance issues, by enhancing visibility and control over cloud resources.
- Third-Party Risks: Managing third-party services effectively requires comprehensive policies that address specific mobile and external service risks, emphasizing the importance of security in vendor relationships.
Leveraging AI and Addressing Its Threats
- AI in Cybersecurity: While AI can significantly enhance threat detection and response, it also presents new challenges as attackers use it to develop sophisticated attack methods.
- Counteracting AI Threats: Organizations must be cautious in deploying AI technologies, ensuring their security systems are prepared to counteract potential AI-driven cyber threats.
Strategic Security Framework Adoption to tackle Cybersecurity Threats
- Zero Trust and JIT Access: Adopting a Zero Trust security paradigm, that inherently distrusts any entity within or beyond the network, coupled with on-demand access, can drastically improve a company’s security stance.
- Continuous Training: As the cybersecurity landscape evolves, ongoing training and development programs are essential to equip cybersecurity professionals with the necessary skills to face emerging threats.
Conclusion
In conclusion, the swift advancement in the cybersecurity field requires a similarly nimble and knowledgeable strategy for protection. The array of threats expected in 2024 – ranging from ransomware to phishing scams, and insider threats – underscores the complex and sophisticated challenges businesses worldwide will encounter.
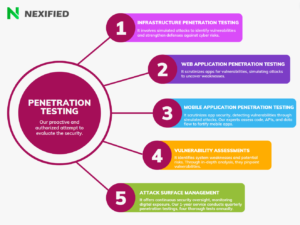
Key strategies for robust defense include integrating AI in cybersecurity, managing insider threats strategically, and implementing advanced protection against ransomware and phishing scams. Given the increasing complexity of cyber threats, it is crucial for businesses to bolster their cybersecurity frameworks. Preemptive measures, including ongoing employee education, cutting-edge threat identification systems, and thorough security evaluations, are vital. The significance of solid strategies like our Pentesting Service is extraordinary in bolstering protections against expected complex cyber intrusions. By maintaining vigilance, strategic planning, and deploying advanced security technologies, businesses can confidently navigate the future cybersecurity landscape, ensuring resilience against looming challenges.
Contact us today for our exceptional Penetration Testing Services to maintain your competitive edge!
FAQs
What are the principal cyber risks anticipated in 2024?
The leading cyber risks for 2024 are Generative AI (GenAI), insecure actions by employees, risks associated with third parties, persistent exposure to threats, communication gaps within corporate boardrooms, and an emphasis on identity-centric security strategies, as identified by Gartner, Inc. Learn about Generative AI here
What cyber security threats should every individual be conscious of?
Every user should be vigilant about various types of cyber threats, including Malware, Ransomware, Distributed Denial of Service (DDoS) attacks, as well as Spam and Phishing schemes.
Can you list the top five Cybersecurity threats?
The top five critical cybersecurity risks include social engineering, third-party exposure, cloud service vulnerabilities, Ransomware attacks, and IoT device threats.
What does the future hold for Cybersecurity in the coming decade?
Over the next five to ten years, the cybersecurity field will increasingly focus on prevention and preparedness. The lessons learned from 2023 emphasize the importance of proactive planning to effectively handle cybersecurity incidents or data breaches.